Why Continuous Assurance Is Now the Backbone of Executive & Board Reporting

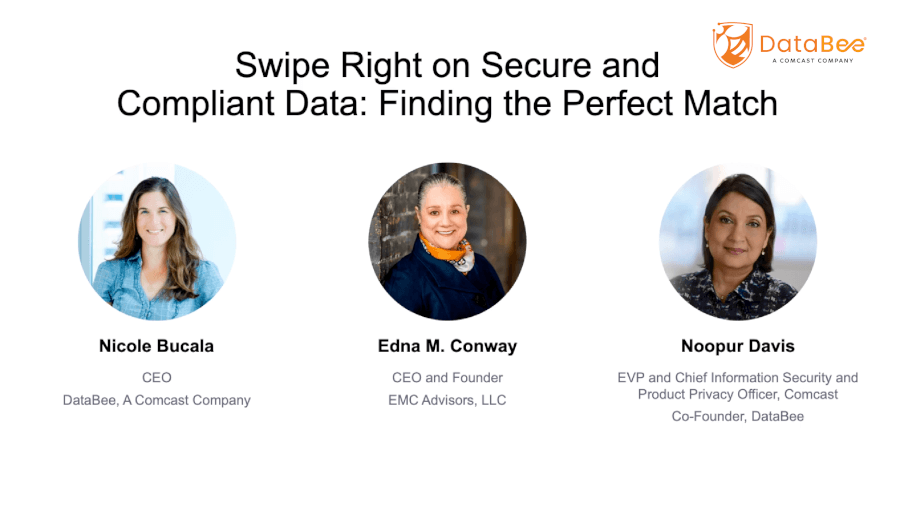
Free the CISO, a podcast series that attempts to free CISOs from their shackles so they can focus on securing their organization, is produced by CIO.com in partnership with DataBee®, from Comcast Technology Solutions.
In each episode, Robin Das, Executive Director at Comcast under the DataBee team, explores the CISO’s role through the position’s relationship with other security stakeholders, from regulators and the Board of Directors to internal personnel and outside vendors.
In our last post, we explored why so many organizations are rethinking traditional compliance approaches—and why periodic checks, manual evidence collection, and siloed tooling no longer meet the needs of modern cybersecurity oversight. As regulations tighten, cyber threats accelerate, and executive teams demand real-time insight; organizations can’t afford security programs that only validate posture once or twice a year.
This second installment focuses on a more specific—and increasingly urgent—challenge: executive and board cyber risk reporting. Because while dashboards and slide decks often get the blame, the real problem runs deeper. Most security leaders aren’t struggling with presentation design. They’re struggling with the credibility, consistency, and defensibility of the data itself.
A new model is emerging—continuous assurance powered by a unified security data fabric—and it’s fundamentally changing how CISOs communicate with leadership and regulators.
The Real Problem with Cyber Risk Reporting Isn’t the Dashboard
Executives, boards, and regulators are all asking a version of the same question:
“Can you prove your security program is working right now—and can you show me the evidence?”
But most organizations can’t answer that with confidence. And it’s not because they lack dashboards. It’s because:
- Their data is fragmented.
- Evidence is inconsistently collected or manually assembled.
- Metrics conflict across tools, teams, or time periods.
- There’s no lineage showing where data came from or how it was validated.
- Reporting still relies on point-in-time snapshots that don’t reflect today’s constantly shifting risk landscape.
Boards don’t just want to know, “Do we have EDR deployed?” They want to know:
- What business risk does this control reduce?
- How does a gap in coverage translate to financial exposure?
- What changed since last quarter—and why?
Meanwhile, regulators now expect defensible, systematic evidence, not policy statements or ad hoc screenshots. Logs, configurations, control testing results, and audit trails must be both continuously collected and continuously validated.
This is where most legacy continuous controls monitoring (CCM) approaches fail—and where a modern security data fabric becomes transformative.
Why Continuous Assurance Requires a Unified Security Data Foundation
A security data fabric, like DataBee, helps solve the core data problem by unifying, normalizing, and connecting all security data—across assets, users, identities, controls, vulnerabilities, and business processes. This provides:
Data Quality and Lineage
Leaders can confidently answer: Where did this metric come from? How was it validated? Has it changed over time?
Chain of Custody for Every Control Signal
Evidence isn’t reconstructed during an audit—it’s continuously collected and continuously governed.
Always-On Assurance Across Frameworks
From NIST CSF to PCI DSS to internal governance models, control status is updated in real time, not quarterly.
Translation of Telemetry into Business Risk
Instead of raw technical dashboards, leaders see metrics tied to financial, operational, and strategic impact.
By continuously connecting data and ensuring its defensibility, organizations can finally produce reporting that meets the needs of executives, boards, and regulators—all at once.
What Executives and Boards Expect Now
Real-Time Visibility
CISOs must give leadership a living, continuous view of risk—not a backward-looking snapshot.
Outcome-Driven Reporting
Boards want clarity. They need to understand how controls impact business risk, not how many agents are deployed.
Credibility and Confidence
With SEC cybersecurity rules, DOJ guidance, and global regulatory scrutiny increasing, boards will only trust data that is traceable, defensible, and validated.
Context-Rich Metrics
Executives need to see controls in the context of business operations:
- Which applications are exposed?
- What processes rely on them?
- What revenue impact would a compromise create?
Continuous assurance enables this level of insight.
What Regulators Expect Now
Regulators increasingly want:
- Logs
- Configurations
- Control testing results
- Enforcement evidence
- Systematic audit trails
And they expect this evidence continuously, not retroactively compiled.
Continuous assurance supports exactly that—proving not just control design but control effectiveness.
How DataBee Delivers Continuous Assurance & Credible Executive Reporting
DataBee’s security data fabric powers continuous assurance by unifying operational, identity, threat, and control data into a single normalized model. For executive and board reporting, DataBee delivers:
Executive-Level Dashboards with Defensible Metrics
Tailored views for CISOs, boards, BISOs, analysts, and other stakeholders—providing clarity for leadership and depth for practitioners.
Data Lineage and Traceability
Every metric includes lineage, validation, and chain of custody, enabling confidence that what is reported can be defended in an audit.
Integrated and Expanding Coverage
Continuous integration across cloud, SaaS, identity, endpoint, and infrastructure sources ensures complete visibility across the security stack.
Risk Flow: AI-Powered Natural-Language Inquiry
Risk Flow—DataBee’s AI interface—lets leaders ask questions in plain language, such as:
- “Why did this control status change last week?”
- “Which vulnerabilities impact our financial systems with the highest potential loss?”
- “Show me the evidence supporting this risk rating.”
The system answers with validated data, evidence, and lineage—helping reduce time spent navigating dashboards and accelerating decision-making.
The Bottom Line
Continuous controls monitoring was the first step. Continuous assurance—powered by unified, trustworthy, defensible security data—is the future.
Boards, executives, and regulators no longer want point-in-time answers.
They want real-time truth.
DataBee’s security data fabric makes that possible, helping teams deliver:
- Real-time visibility
- Risk translation
- Continuous evidence
- Credible, defensible executive reporting
And ultimately, a security program that leadership can trust—and confidently act on.
Want to See the Full Discussion?
Watch the full video now: From Continuous Controls Monitoring to Continuous Assurance
Additional Resources
DataBee | 3 Key Components for Continuous Compliance & Risk Management | Webinar Insights
DataBee | Cybersecurity Compliance with Continuous Controls Monitoring | DataBee® Webinar
More posts


Entity resolution connects users, devices, and applications into trusted data—enabling accurate security data correlation, detection, and compliance at scale.


Discover how to streamline vulnerability management, improve asset visibility, and reduce security risks. Learn from Comcast and DataBee experts in this webinar.

Overwhelmed by security data? Learn how to manage it effectively, reduce risk, and boost compliance in this expert-led webinar from DataBee and Comcast.
Discover what DataBee® can do for you

Developed and proven at scale, DataBee® delivers connected security and compliance data and insights that can work for everyone in your organization

Built to protect critical government and enterprise networks, BluVector delivers AI-powered NDR for visibility across network, devices, users, files and data to discover and hunt skilled and motivated threat actors


